I. Introduction: The SME SaaS Dilemma — Balancing Compliance and Resource Realities
Modern software engineering presents a paradox for mid-sized SaaS providers. To stay competitive, these companies adopt complex distributed systems and hybrid clouds. However, securing these environments requires significant human capital. In many Small-to-Medium Enterprises (SMEs), a dedicated security team is a luxury. Instead, security duties often fall on DevOps engineers or developers.
A common industry fallacy suggests that total cloud adoption is the only path to security. In reality, a fully public cloud footprint often leads to rising costs and a fragmented attack surface. A more rational approach is a Strategic Hybrid Cloud model. This strategy decouples computing tasks from data storage. By keeping sensitive data with top-tier cloud providers, companies leverage massive global security investments. Meanwhile, moving heavy computing workloads to local managed environments, such as Proxmox, ensures better control. This “Cloud-Exit” strategy can reduce monthly infrastructure costs by up to 80% without losing scalability.
However, running deployment tools in a local environment introduces a new challenge. How can a local runner perform high-privilege tasks without creating a security hole? The first line of defense is a shift in authorization logic. GitHub Self-hosted Runners eliminate external threats by using a “Pull” model instead of “Pushing” data from the internet. But the real battle happens inside the runner itself. This article explores why standard global permissions are a liability and how a granular execution policy creates a hardened, defensive pipeline.
II. Implementation: The Battle of Privileges — su - vs. visudo
In a hybrid CI/CD pipeline, the runner often needs elevated permissions to manage system services, reload configurations, or synchronize files to restricted directories. However, granting these permissions incorrectly creates a significant security vulnerability. If an attacker compromises a deployment script, they could potentially gain full control over the local host.
The Risk of Global Escalation (su -)
Many teams take a shortcut by allowing the runner to use su - or providing a broad sudo ALL configuration in the environment. This approach is a liability for several reasons:
- Lack of Traceability: When a runner executes commands as a root user, it becomes nearly impossible to audit which specific pipeline action triggered a system change.
- Lateral Movement: If the runner process is hijacked, the attacker inherits unrestricted access to the entire operating system, bypassing any intended resource isolation.
- Credential Exposure: Storing high-privilege passwords within environment variables—even as “Secrets”—increases the risk of accidental leaks during verbose log outputs.
The Solution: Granular Behavior Definition via visudo
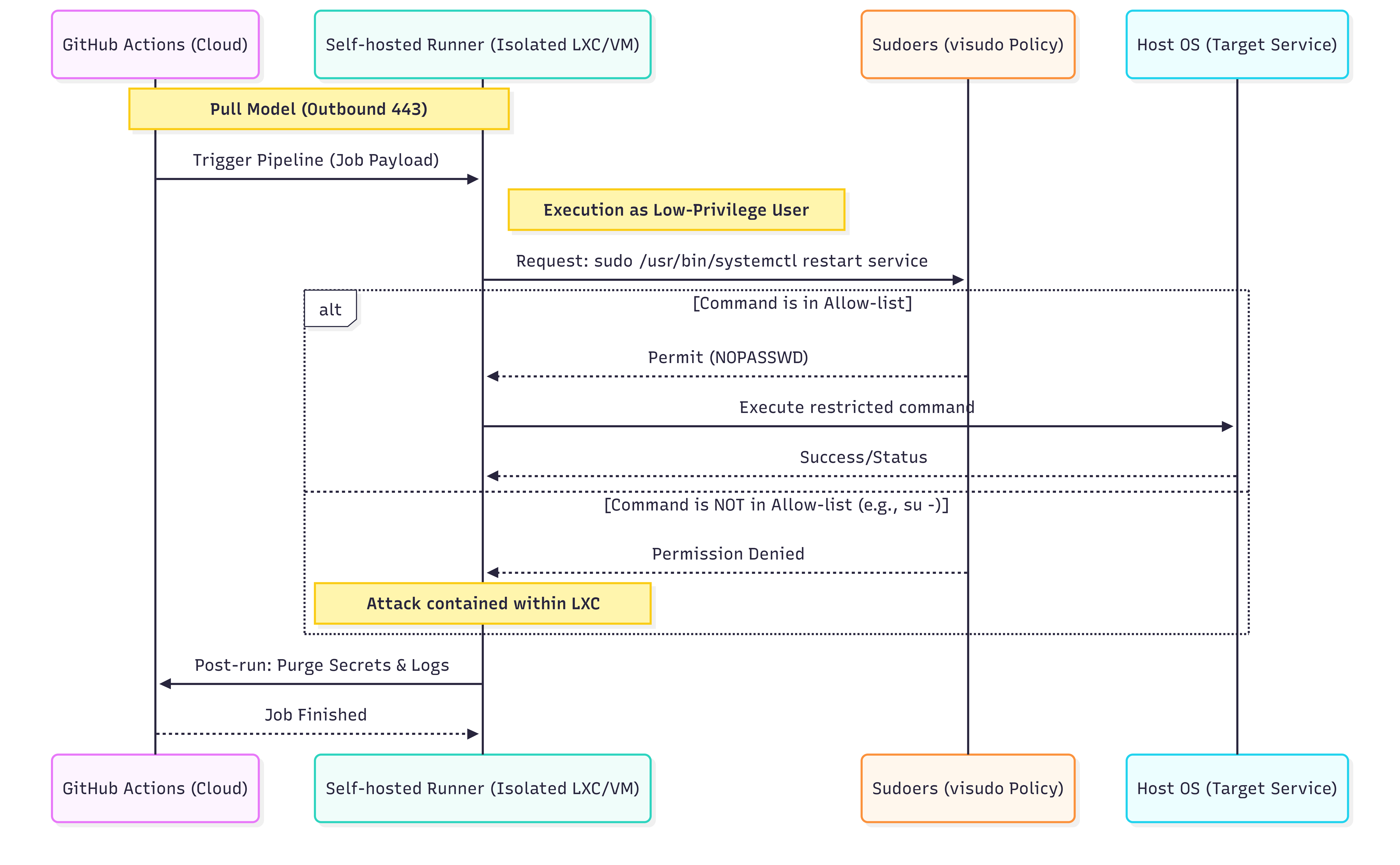
A more secure and professional implementation uses the visudo utility to safely edit the sudoers file. Instead of granting total power, the administrator defines a strict “allow-list” of specific commands that the runner is permitted to execute without a password.
For example, a runner may only need to restart a specific web service or move files to a designated production folder. By restricting the runner to these pre-defined binary paths, the attack surface is minimized. Even if a pipeline is compromised, the damage is contained within the boundaries of those specific, non-destructive commands.
This strategy, which I have implemented to secure multi-tenant platforms, ensures that the runner operates under the Principle of Least Privilege (PoLP). When combined with LXC or VM isolation, this creates a multi-layered defense that protects the core infrastructure while maintaining deployment agility.
III. Extension & Comparison: From CI/CD to Minimalist Engineering
The security logic applied to GitHub Runners is a practical demonstration of Minimalist Engineering in DevOps. This philosophy prioritizes the simplest, most direct solution to a technical requirement over the adoption of complex, high-overhead tooling. In the context of small-to-medium SaaS providers, “fancy” or “all-in-one” toolsets often introduce unnecessary layers of abstraction that can obscure security vulnerabilities rather than solve them.
The Principle of Minimalist Engineering
Minimalist Engineering is not about a lack of sophistication; it is about architectural discipline. It advocates for:
- Reduced Complexity: Avoiding “tool sprawl” where multiple platforms overlap in functionality, increasing the maintenance burden.
- Direct Resolution: Using native OS capabilities to enforce security at the kernel and filesystem level.
- Proven Reliability: Relying on stable, time-tested Unix philosophies to meet compliance and safety standards.
Case Studies: Matching Tools to Tasks
It is important to recognize that Ansible is an exceptionally powerful tool for large-scale configuration management and complex multi-node orchestration. However, in many operational scenarios, the most effective solution is the one with the fewest moving parts:
- Routine Maintenance and Scheduled Tasks: Most daily operational tasks and periodic maintenance can be efficiently handled via a CI/CD Pipeline + Pre-defined visudo behaviors. This model is straightforward to manage and maintains a high security posture by keeping permissions localized. For these specific, repetitive tasks, the infrastructure does not necessarily require the full weight of a global orchestration engine.
- System Monitoring (e.g., Zabbix): In monitoring environments, using visudo allows a Zabbix agent to execute required scripts without granting the agent excessive system privileges. By defining precise binary paths in the configuration, the monitoring service remains functional yet strictly confined, ensuring that even a compromised agent cannot be used for unauthorized lateral movement.
By applying Minimalist Engineering, teams focus on Results over Tooling. This approach ensures that the infrastructure remains lean, auditable, and secure by aligning the tool’s complexity with the task’s actual requirements.
(Note: While this article focuses on lean alternatives for specific tasks, I will be publishing a follow-up piece soon exploring the advanced application of Ansible in Modern SaaS Architectures, specifically regarding large-scale cluster orchestration and stateful service management.)
IV. Conclusion: Engineering Resilience through Minimalist Authorization
This article has explored the strategic transition to a hybrid cloud model, focusing on the security of GitHub Self-hosted Runners within an on-premise environment. We analyzed the shift from high-risk global escalation (su -) to granular, behavior-based authorization using visudo, and how this local control effectively secures the pipeline against lateral movement. By decoupling compute from storage and enforcing the Principle of Least Privilege (PoLP) at the OS level, organizations can maintain a hardened DevSecOps posture while significantly reducing infrastructure overhead.
The core philosophy driving these architectural choices is Minimalist Engineering in DevOps. This approach advocates for using the simplest, most direct tools to solve complex problems—prioritizing stable, native OS capabilities over unnecessarily “fancy” or over-engineered orchestration. True resilience is not found in the complexity of a toolset, but in the discipline of a lean architecture that aligns every technical action with a specific, authorized purpose.

