by Chris | Jan 9, 2026 | Blog
I. Introduction The landscape of software engineering has undergone a tectonic shift over the last decade. Historically, an application might have resided on a single monolithic server with a predictable relational database. Today, we operate in an era of...
by Chris | Jan 7, 2026 | Blog
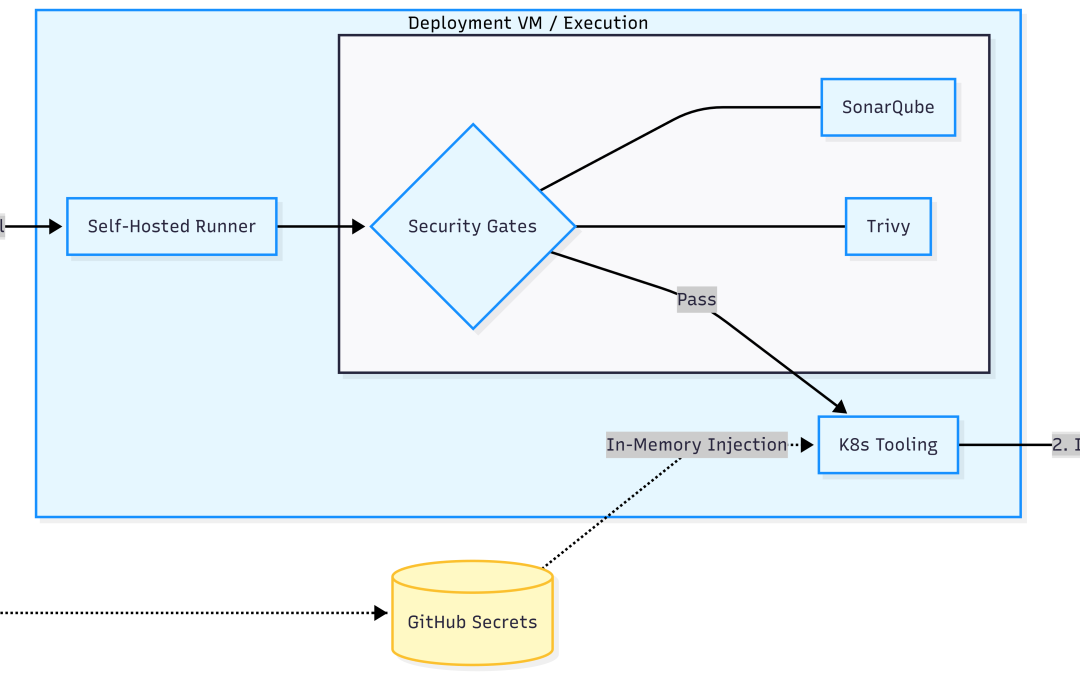
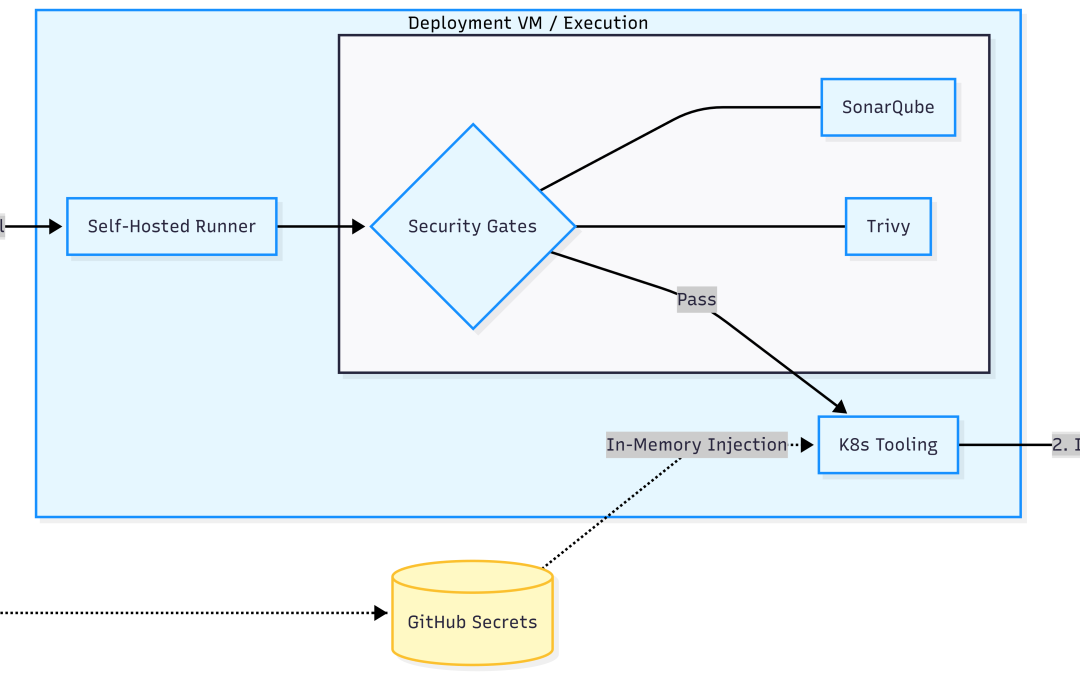
In Part 1, we established the “Frontline” of our SaaS—a hardened perimeter consisting of DMZ isolation and Layer 7 WAF scrubbing. However, a secure boundary is only half the battle. In a Modern SaaS environment, the greatest risk often lies in how we build...
by Chris | Jan 4, 2026 | Blog
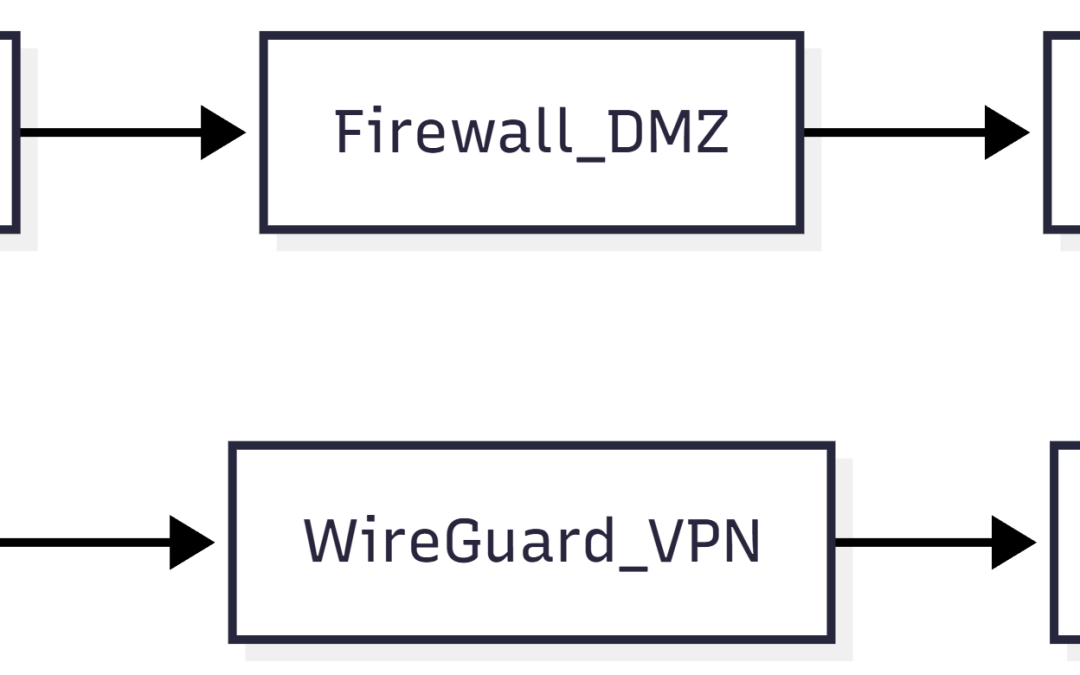
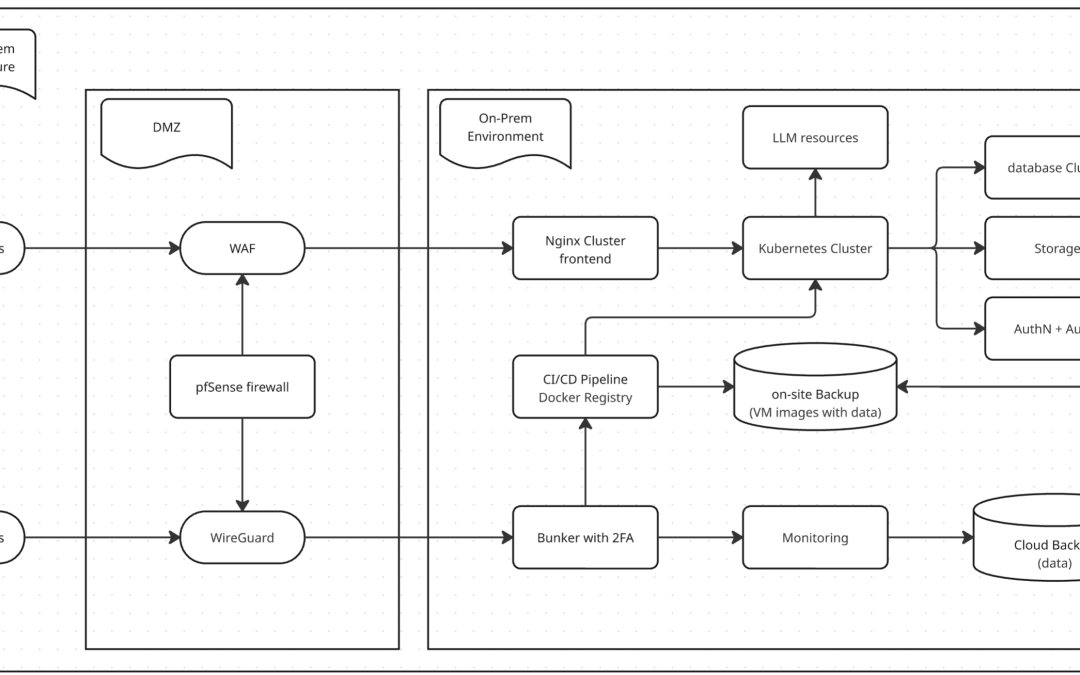
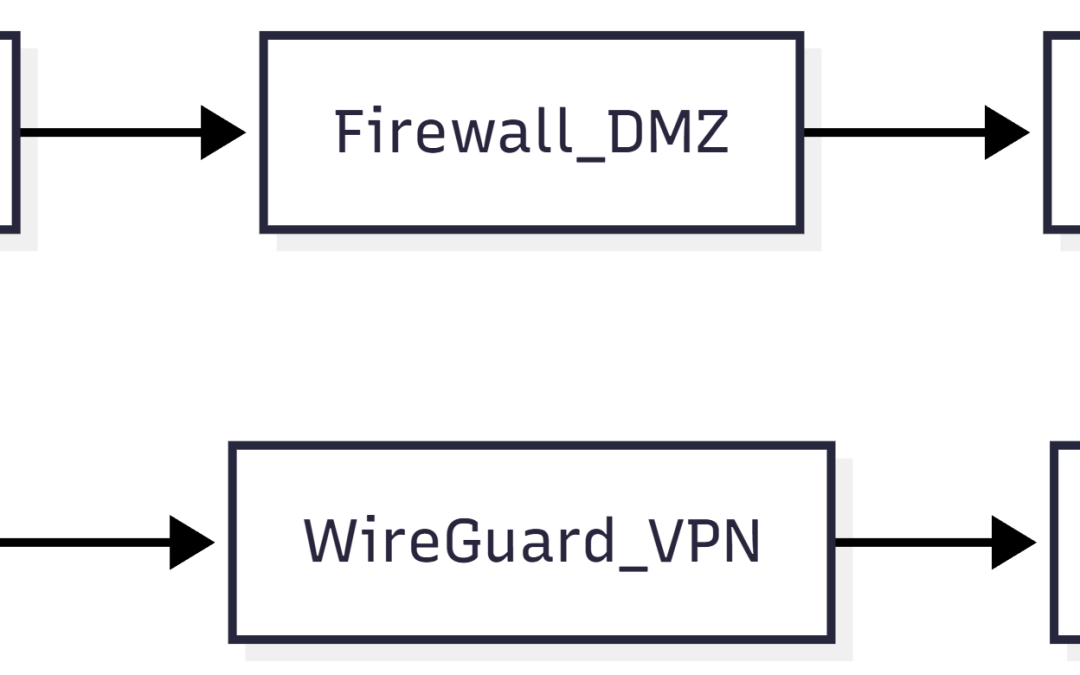
Introduction: The Trinity of the SaaS Frontline For a modern SaaS provider, the “Frontline” is not a single device. It is a strategic security complex that separates core data assets from the chaos of the internet and from the risks inside the corporate office. Many...
by Chris | Jan 3, 2026 | Blog
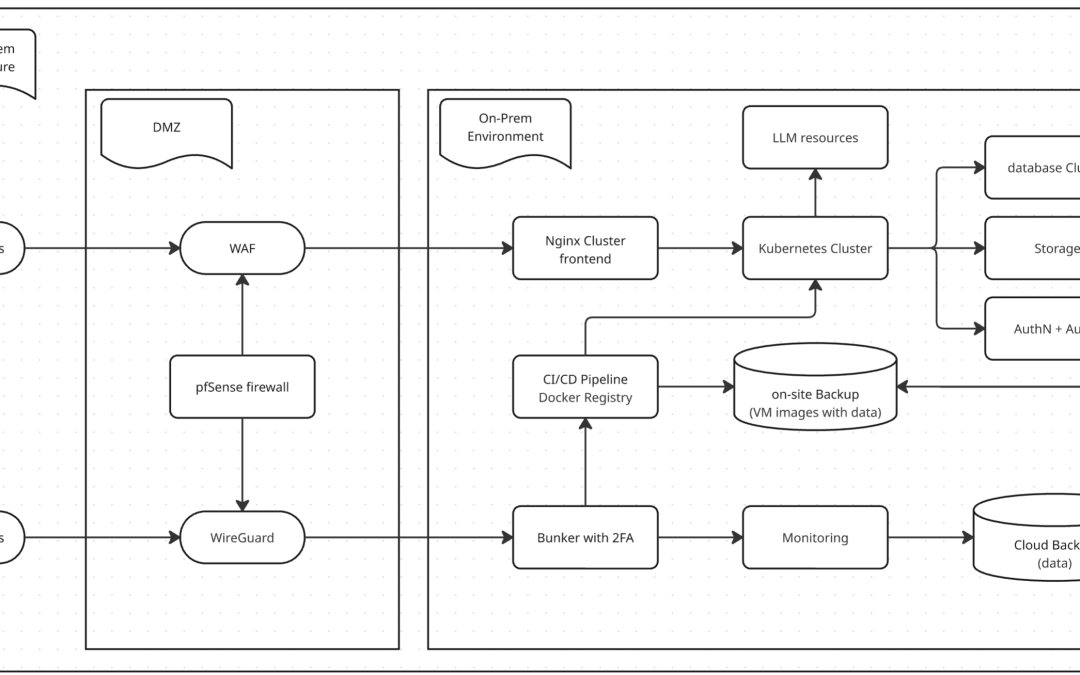
For organizations building a Modern SaaS, the architectural choice is often a painful compromise. Public cloud costs for compute are skyrocketing, yet pure on-premise environments often lack the security rigor and durability required for enterprise-grade compliance....

by Chris | Dec 31, 2025 | Blog
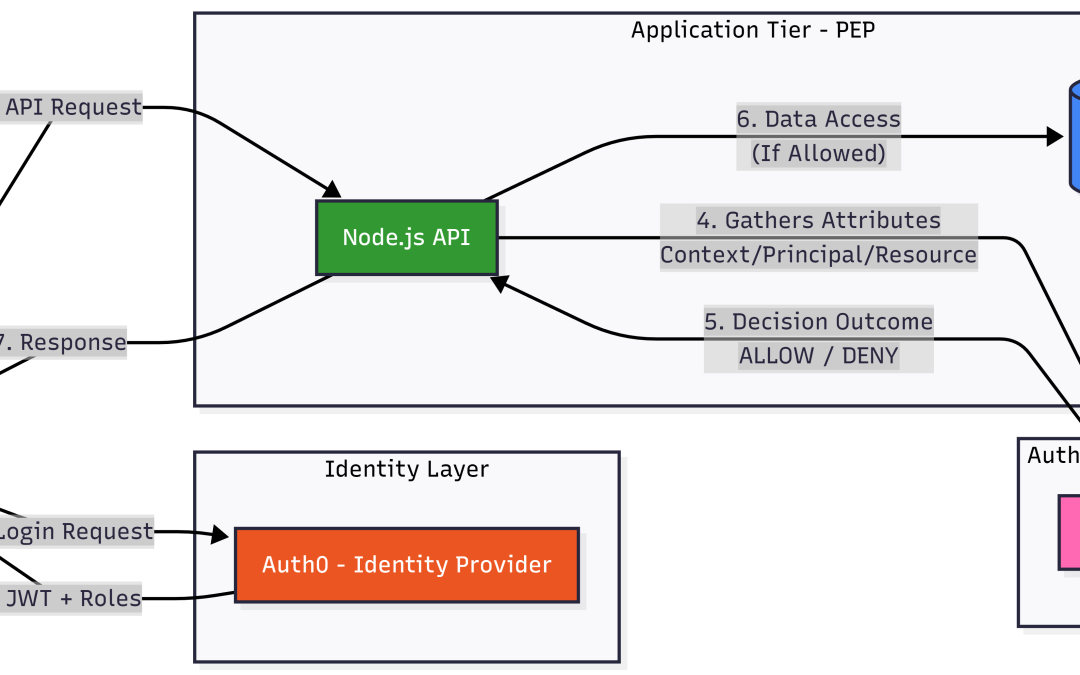
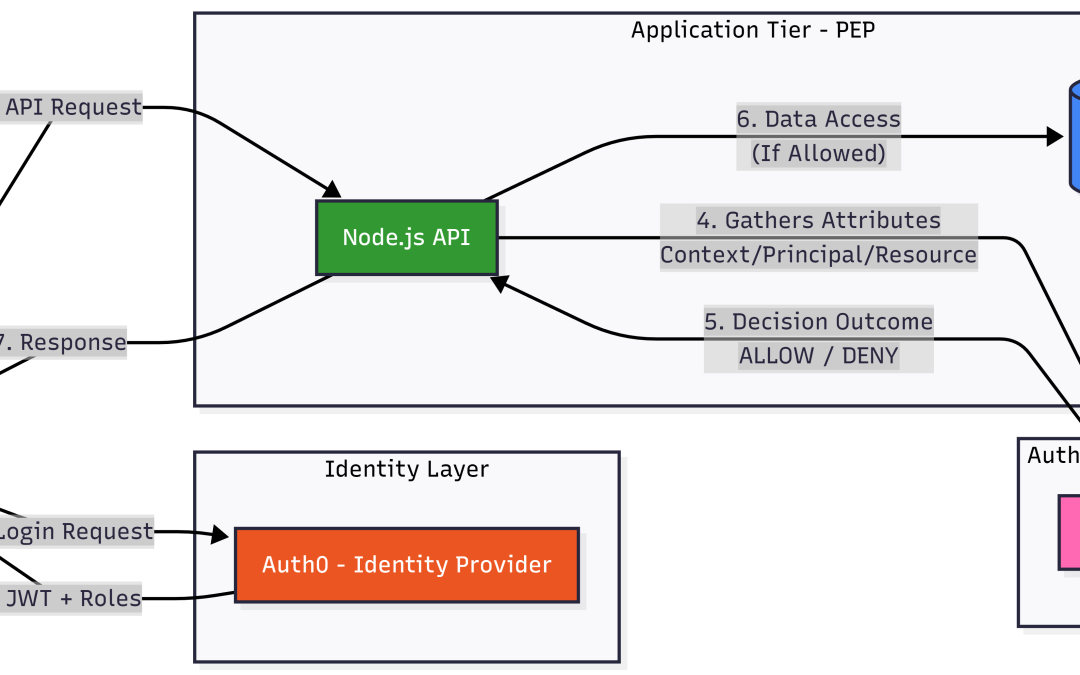
In the rapidly evolving landscape of Cloud-Native development, the intersection of Multi-Tenant SaaS and Large Language Model (LLM) integration has introduced unprecedented complexity to access control. As organizations shift from monolithic structures to distributed...
by Chris | Dec 28, 2025 | Blog
Introduction: The Invisible Crisis of Authorization Silos In the modern distributed landscape, OWASP A01: Broken Access Control has ascended to the top of the security threat hierarchy for a reason. As enterprises move from centralized monoliths to sprawling...